What is Wardriving?
What is wardriving?
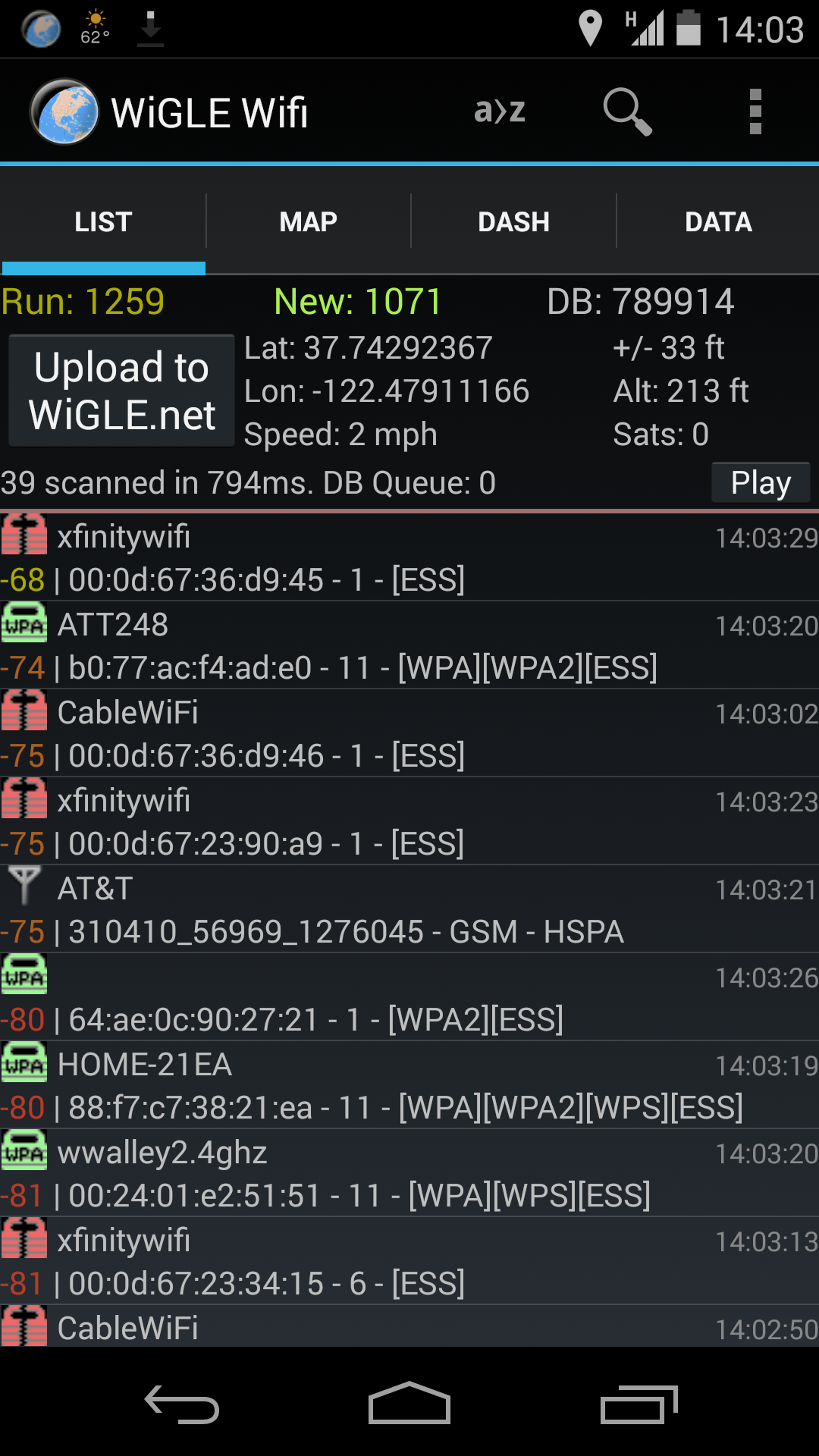
Wardriving is a technique by hackers and security experts to conduct large-scale surveillance of networks by simply driving by their signals and recording the information. It is also a game played among many of them to see who can collect the most network-data. It starts with downloading an app such as G-MoN or Wigle. Once the app is installed and an account is setup, the individual only needs to drive around and it will automatically capture the information being broadcasted by wireless devices. These devices can be wireless access points, wireless printers, Bluetooth devices, and home automation systems.
Why is it important to hackers and security experts?
By scanning for devices on such a large scale, it allows for one to determine the most vulnerable devices in a region. Hackers use this to exploit the weakest links in their list (usually WEP secured networks), while security experts use it to reduce the number of vulnerabilities that could potentially affect their clients. These weak links can be used as a platform for attack to other parts of a network. The most common of these are wireless printers, however, due to the rise of automation it is very likely that Bluetooth devices will be next on that list.
Tips on how to prevent being targeted by wardrivers?
While it is not entirely possible to prevent being wardriven, you can take the following steps to secure yourself better:
- Do not broadcast your printer using the wireless function, instead connect it to your current Wi-Fi which may be more secure.
- Do not broadcast Bluetooth devices until you are ready to use them. If they are for home automation, review the security settings on the device and have a technician configure any changes.
- Do not use WEP, WPS, or WPA. Currently, we recommend using WPA2 with AES encryption (or higher) and only use WPS for devices that are not being broadcasted in order to prevent spoofing.
- Use a strong password that is at least 16 characters long and has complexity.